FreeRADIUS is an open-source, scalable, modular, and high-performance RADIUS protocol server. FreeRADIUS is in fact the most popular and widely deployed RADIUS server.
It’s used mainly to perform AAA i.e. Authorisation, Authentication, Accounting services on various types of network access.
It works as a daemon on UNIX and UNIX-like operating systems.
The FreeRADIUS server connects and talks with a client including Ethernet switches, Wireless access points, terminal servers, or a PC configured with the appropriate software (radiusclient, PortSlave, etc).
In this article, we’ll explain the step-by-step process of installing FreeRADIUS and DaloRADIUS on CentOS 8 with MySQL or MariaDB.
Table of Contents
Prerequisites
- A server running CentOS 8
- We recommend acting as a
non-root sudo user. This is because if you are logged in as root you can easily destroy your system if you’re not careful.
We will be using DNF (Dandified YUM) instead of YUM. DNF is the default package manager for Fedora 22, CentOS 8, and RHEL 8 distributions. DNF is the next-generation version intended to replace yum in RPM-based systems. It’s a powerful package manager and capable of automatically resolving dependency issues.
Update package index:
sudo dnf -y update
Video Version of this Tutorial
We’ve also included the video version of this tutorial, where go through it from start to finish. This may help in case there’s situations where the writing seems unclear and it’s easier to follow by watching us go through the steps.
sudo cp /var/www/html/daloradius/library/daloradius.conf.php.sample /var/www/html/daloradius/library/daloradius.conf.php to create the file, and then you can continue following the tutorial. This written guide has also been updated to reflect the changes to daloRADIUS.Skip the setup and instantly deploy a pre-configured FreeRADIUS server with MySQL and daloRADIUS in seconds. Our solution is secure, fully configured, and designed to save you time.
Your servers, managed for you, so you can focus on your business.
Need a custom solution? Our expert team is available for hire. Feel free to contact us.
Install LAMP Stack on CentOS 8
LAMP stack is a set of open-source softwares that can be used to create web applications and websites. LAMP stands for its original components Linux, Apache, MySQL, PHP. The LAMP stack is no longer limited to the original open-source components.
Install Apache Web Server
Install the httpd package:
sudo dnf install httpd
Press Y and ENTER if prompted.
Start Apache and enable it so it starts on boot:
sudo systemctl start httpd sudo systemctl enable --now httpd
If you have firewall enabled, we need to enable HTTP connections to Apache:
sudo firewall-cmd --permanent --add-service={http,https}
Reload it to apply the changes:
sudo firewall-cmd --reload
Check if Apache is running by visiting your server’s IP address (with HTTP, not HTTPS), you should see something like this:
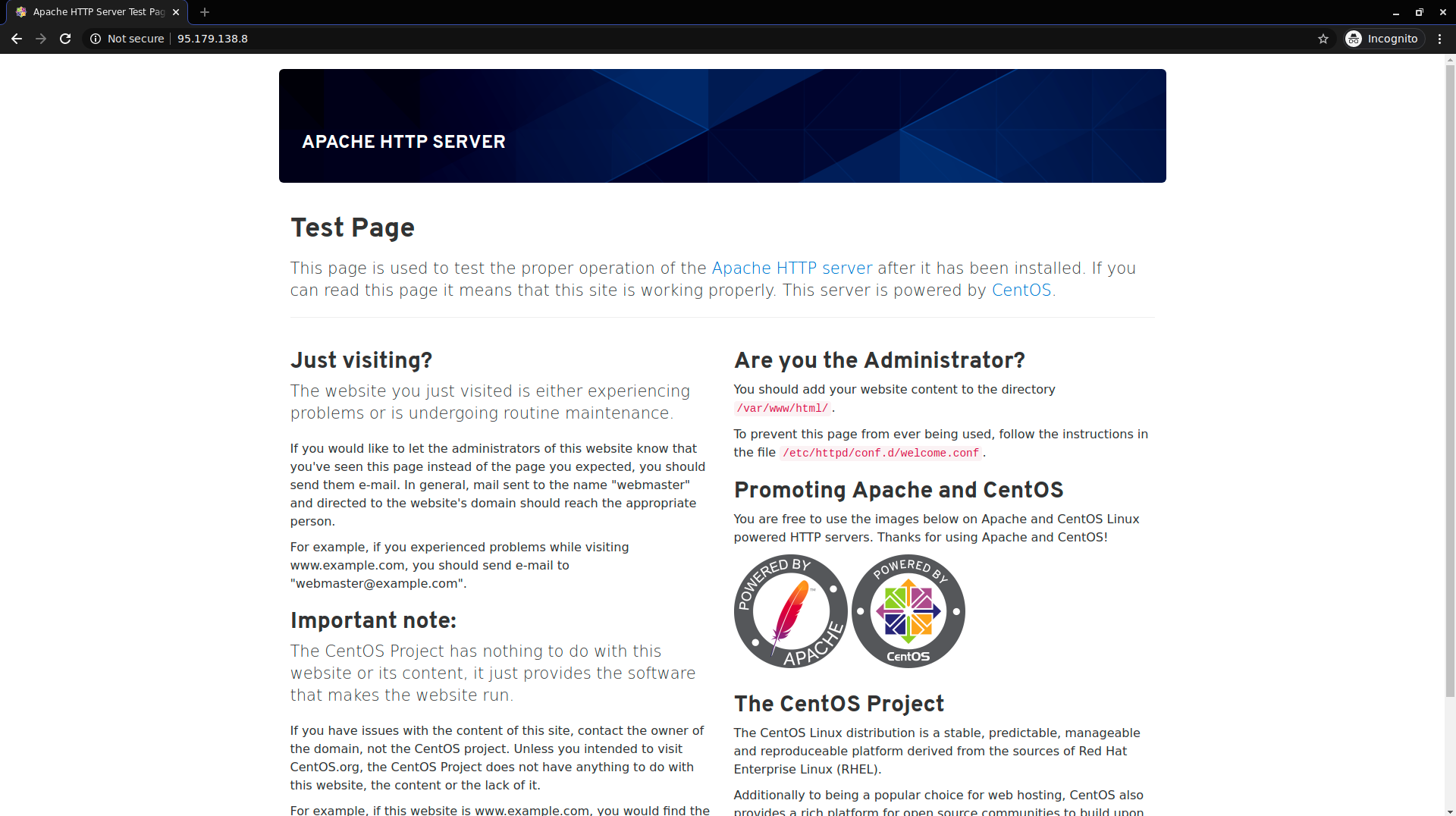
Make sure to visit http://your_ip and not https://your_ip. If you get an error check the address you’re visiting, because your browser might have added https:// instead of http://
Install MySQL / MariaDB
sudo dnf -y install mariadb-server sudo systemctl start mariadb
Now we’ll run a script that MariaDB ships with, which takes us through some steps to improve our MariaDB security options:
sudo mysql_secure_installation
You’ll be taken through a series of prompts. We recommend you fill them out as follows:
Unless you know you set a password, just press enter when prompted:
Enter current password for root (enter for none): Enter
Next confirm that you want to set a new root password and set a strong password:
Setting the root password ensures that nobody can log into the MariaDB root user without the proper authorisation. Set root password? [Y/n] Y New password: Y0ur_Str0ng_Passw0rd Re-enter new password: Y0ur_Str0ng_Passw0rd Password updated successfully! Reloading privilege tables.. ... Success!
Next you can just press ENTER for the prompts that follow (unless you have other plans in mind that we don’t cover in this tutorial).
Remove anonymous users:
Remove anonymous users? [Y/n] y ... Success!
Disallow root login remotely:
Disallow root login remotely? [Y/n] y ... Success!
Remove test database:
Remove test database and access to it? [Y/n] y - Dropping test database... ... Success! - Removing privileges on test database... ... Success!
Reload privilege tables:
Reload privilege tables now? [Y/n] y ... Success! Cleaning up...
Now MariaDB (or MySQL) should be successfully set up on your machine.
Install PHP
Install PHP 7.3 / PHP 7.4 on CentOS 8 (Optional)
The default version distributed with CentOS 8 is PHP7.2. If you want to install PHP 7.2, then you can skip this step.
Enable the Remi Repository
sudo dnf install -y dnf-utils http://rpms.remirepo.net/enterprise/remi-release-8.rpm
sudo dnf module list php sudo dnf module reset php
Install PHP 7.3
sudo dnf module enable php:remi-7.3
Install PHP 7.4
sudo dnf module enable php:remi-7.4
Enable the PowerTools repository, as some packages may depend on some of its packages:
sudo dnf config-manager --set-enabled PowerTools
Install PHP and some popular PHP extensions:
sudo dnf -y install @php
sudo dnf -y install php-{common,opcache,cli,gd,curl,mysqlnd,devel,pear,mbstring,xml}
sudo systemctl enable --now php-fpm
If you also intend to install daloRADIUS, the freeRADIUS GUI, you’ll also need to install PEAR, a PHP extension, from which we’ll install some dependencies.
sudo dnf -y install php-pear
Next we install the DB and MDB2 libraries from the PEAR repository. These are required by daloRADIUS to work.
sudo pear install DB MDB2
Install freeRADIUS and Configure with MySQL/MariaDB on CentOS 8
Install FreeRADIUS
Use the dnf module list command to list the modules available to our system related to freeradius.
sudo dnf module list freeradius
You should see something like this:
CentOS-8 - AppStream 37 kB/s | 4.3 kB 00:00 CentOS-8 - Base 39 kB/s | 3.9 kB 00:00 CentOS-8 - Extras 17 kB/s | 1.5 kB 00:00 CentOS-8 - AppStream Name Stream Profiles Summary freeradius 3.0 [d][e] server [d] [i] High-performance and highly configurable free RADIUS server Hint: [d]efault, [e]nabled, [x]disabled, [i]nstalled
Install the FreeRADIUS module, FreeRADIUS client utilities, and the MySQL module for FreeRADIUS.
sudo dnf install -y @freeradius freeradius-utils freeradius-mysql
Start the RADIUS service:
sudo systemctl enable --now radiusd.service
Check the status of the service to make sure it’s active and there are no issues so far:
systemctl status radiusd.service
Example output:
● radiusd.service - FreeRADIUS high performance RADIUS server. Loaded: loaded (/usr/lib/systemd/system/radiusd.service; enabled; vendor preset: disabled) Active: inactive (dead) since Fri 2020-06-12 07:28:35 UTC; 5h 23min ago Process: 8163 ExecStart=/usr/sbi/radiusd -d /etc/raddb (code=exited, status=0/SUCCESS) Process: 8160 ExecStartPre=/usr/sbin/radiusd -C (code=exited, status=0/SUCCESS) Process: 8158 ExecStartPre=/bin/chown -R radiusd.radiusd /var/run/radiusd (code=exited, status=0/SUCCESS) Main PID: 8166 (code=exited, status=0/SUCCESS) Jun 12 07:21:21 bytexdradius systemd[1]: Starting FreeRADIUS high performance RADIUS server.... Jun 12 07:21:21 bytexdradius systemd[1]: Started FreeRADIUS high performance RADIUS server..
Configure CentOS 8 Firewall for FreeRADIUS
We’ll need to configure Firewalld to allow radius packets.
RADIUS uses ports 1812 for authentication and port 1813 for accounting, so we’ll need to allow traffic on these ports. Upon installing FreeRADIUS, it added it’s configuration to firewalld, so to allow radius traffic in and out run the following command:
sudo firewall-cmd --add-service=radius --permanent
Reload the firewall for changes to take effect:
sudo firewall-cmd --reload
You can check the configuration file added by FreeRADIUS to Firewalld by running:
cat /usr/lib/firewalld/services/radius.xml
Example output:
RADIUS The Remote Authentication Dial In User Service (RADIUS) is a protocol for user authentication over networks. It is mostly used for modem, DSL or wireless user authentication. If you plan to provide a RADIUS service (e.g. with freeradius), enable this option.
Confirm that the changes have been successfully added to the default zone. The services we mainly want to see are http, https, and radius.
$ sudo firewall-cmd --get-default-zone public $ sudo firewall-cmd --list-services --zone=public cockpit dhcpv6-client http https radius ssh
The services we allowed so far in this guide (http, https, and radius) are listed in the output, so we can proceed.
Test the RADIUS Server
To test that FreeRADIUS works we’ll run it in debug mode. To do this we’ll first have to stop the current running process. If we run it in debug mode while the other process is still running, then we’ll get an error.
To stop the current process stop the service by running:
sudo systemctl stop radiusd.service
Run the RADIUS server in debug mode:
sudo radiusd -X
You should get an output ending in:
... Listening on auth address 127.0.0.1 port 18120 bound to server inner-tunnel Listening on auth address * port 1812 bound to server default Listening on acct address * port 1813 bound to server default Listening on auth address :: port 1812 bound to server default Listening on acct address :: port 1813 bound to server default Listening on proxy address * port 33167 Listening on proxy address :: port 57427 Ready to process requests
If the output looks good then stop debug mode by pressing Ctrl+C, and start the service again by running:
sudo systemctl start radiusd.service
Configure freeRADIUS to use MySQL/MariaDB
Now we’ll configure MySQL/MariaDB for FreeRADIUS.
First we’ll create a database and a database user for FreeRADIUS, then create a database, and a user identified by a password.
In this example we’ll use the following details:
Database: radius
User: radius
Password: Somestrongpassword_321
You can replace the names and password with whatever you like, but you’ll have to pay attention in configurations we’ll do later on, to appropriately replace values.
Start by accessing the MySQL/MariaDB console as root:
mysql -u root -p
Run the commands to create the database and user:
MariaDB [(none)]> CREATE DATABASE radius; MariaDB [(none)]> GRANT ALL ON radius.* TO radius@localhost IDENTIFIED BY "Somestrongpassword_321"; MariaDB [(none)]> FLUSH PRIVILEGES; MariaDB [(none)]> quit;
Next import the RADIUS MySQL schema into the newly created database:
sudo su - mysql -u root -p radius < /etc/raddb/mods-config/sql/main/mysql/schema.sql
Create a soft link for SQL under /etc/raddb/mods-enabled/
sudo ln -s /etc/raddb/mods-available/sql /etc/raddb/mods-enabled/
Now we’ll configure FreeRADIUS to use MySQL. We do this by editing the file /etc/raddb/mods-available/sql. You can use your favorite text editor. I’ll install and use nano:
sudo dnf install -y nano sudo nano /etc/raddb/mods-available/sql
The file is long, due explanations and lines that are commented out, but we’ll just edit a few lines:
- Change
driver = "rlm_sql_null"todriver = "rlm_sql_mysql" - Change
dialect = "sqlite"todialect = "mysql" - When configuring FreeRADIUS to work with MySQL, we’ll find that the MySQL configuration assumes we’ll use TLS by default. For the purposes of this tutorial we won’t be using SSL certificates, so we will comment out the TLS section. To do this we’ll have to find this section in the file and comment it out. Here it is in its initial state:
mysql { # If any of the files below are set, TLS encryption is enabled tls { ca_file = "/etc/ssl/certs/my_ca.crt" ca_path = "/etc/ssl/certs/" certificate_file = "/etc/ssl/certs/private/client.crt" private_key_file = "/etc/ssl/certs/private/client.key" cipher = "DHE-RSA-AES256-SHA:AES128-SHA" tls_required = yes tls_check_cert = no tls_check_cert_cn = no } # If yes, (or auto and libmysqlclient reports warnings are # available), will retrieve and log additional warnings from # the server if an error has occured. Defaults to 'auto' warnings = auto }And this is how it looks with the tls section commented out:
mysql { # If any of the files below are set, TLS encryption is enabled # tls { # ca_file = "/etc/ssl/certs/my_ca.crt" # ca_path = "/etc/ssl/certs/" # certificate_file = "/etc/ssl/certs/private/client.crt" # private_key_file = "/etc/ssl/certs/private/client.key" # cipher = "DHE-RSA-AES256-SHA:AES128-SHA" # tls_required = yes # tls_check_cert = no # tls_check_cert_cn = no #} # If yes, (or auto and libmysqlclient reports warnings are # available), will retrieve and log additional warnings from # the server if an error has occured. Defaults to 'auto' warnings = auto } - Uncomment server, port, login, and password, and also change some of their values.They initially look like this:
# Connection info: # # server = "localhost" # port = 3306 # login = "radius" # password = "radpass" # Database table configuration for everything except Oracle radius_db = "radius"
Change them by uncommenting them and changing their values to correspond to the database and user you created earlier:
# Connection info: # server = "localhost" port = 3306 login = "radius" password = "Somestrongpassword_321" # Database table configuration for everything except Oracle radius_db = "radius"
- Uncomment the line containing
read_clients = yes, by removing the # symbol at the beginning of the line. - Save the file. If you’re using nano then press
Ctrl+XandENTERto save the file and exit.
Now change the group rights of the file we just edited to radiusd:
sudo chgrp -h radiusd /etc/raddb/mods-enabled/sql
And restart the radiusd service:
sudo systemctl restart radiusd
Since we’ve made significant changes, we’ll test again in debug mode to make sure FreeRADIUS is working.
Stop the radiusd service:
sudo systemctl stop radiusd
And run it in debug mode:
sudo radiusd -X
You should get a long output ending in something like:
Listening on auth address 127.0.0.1 port 18120 bound to server inner-tunnel Listening on auth address * port 1812 bound to server default Listening on acct address * port 1813 bound to server default Listening on auth address :: port 1812 bound to server default Listening on acct address :: port 1813 bound to server default Listening on proxy address * port 45059 Listening on proxy address :: port 54555 Ready to process requests
Now FreeRADIUS is installed and working with MySQL or MariaDB on your CentOS 8 server.
The following steps are to install daloRADIUS, a FreeRADIUS web panel. As such, these are optional, and only if you want to use the web panel.
Install & Configure daloRADIUS (FreeRADIUS GUI) on CentOS 8 (Optional)
daloRADIUS is an advanced RADIUS web management application. It’s aimed at managing hotspots and general-purpose ISP deployments. It offers multiple excellent features like a powerful graphic interface, advanced user management, billing engine, integration with Google Maps, and more.
Install wget
sudo dnf -y install wget
Download the daloRADIUS from Github:
cd /tmp && wget https://github.com/lirantal/daloradius/archive/master.zip
Install unzip if you don’t already have it, unzip the daloRADIUS archive, and move it into the DocumentRoot.
Document root file is the folder where website files for a specific domain are stored. It’s important to have a unique folder for each domain as cPanel allows for multiple domains (subdomains and add-on domains).
After installation of Apache, the document root file is located at the /var/www/html/ by default but we can change the location of the directory later.
sudo dnf -y install unzip unzip master.zip sudo mv daloradius-master/ /var/www/html/daloradius
Navigate via cd in the daloradius folder /var/www/html/daloradius so we can easily import daloRADIUS MySQL tables:
cd /var/www/html/daloradius mysql -u root -p radius < contrib/db/fr2-mysql-daloradius-and-freeradius.sql mysql -u root -p radius < contrib/db/mysql-daloradius.sql
Now change the ownership of the daloradius folder to the Apache webserver.
sudo chown -R apache:apache /var/www/html/daloradius/
Next we’ll need to create our daloRADIUS configuration file. We’re provided with a sample of such a configuration file, that we’ll need to copy and change it’s name. The sample file is called /var/www/html/daloradius/library/daloradius.conf.php.sample and to create the file we’ll run the following command to copy and rename it:
sudo cp /var/www/html/daloradius/library/daloradius.conf.php.sample /var/www/html/daloradius/library/daloradius.conf.php
And we’ll also make the daloradius.conf.php configuration file writable by the webserver.
sudo chmod 664 /var/www/html/daloradius/library/daloradius.conf.php
Open the daloradius.conf.php configuration file so we can edit MySQL information:
sudo nano /var/www/html/daloradius/library/daloradius.conf.php
Change the values to your database user/password/database name:
$configValues['CONFIG_DB_HOST'] = 'localhost'; $configValues['CONFIG_DB_PORT'] = '3306'; $configValues['CONFIG_DB_USER'] = 'radius'; $configValues['CONFIG_DB_PASS'] = 'Somestrongpassword_321'; $configValues['CONFIG_DB_NAME'] = 'radius';
Press Ctrl+X and ENTER to save and exit, if you’re using nano to edit the file.
Restart the radiusd service and check it’s status to make sure it’s working.
sudo systemctl restart radiusd.service httpd systemctl status radiusd.service httpd
By default, CentOS 8 has SELinux enabled and in enforcing mode.
SELinux (Security-Enhanced Linux) is a Linux Kernel security module. It gives administrators more control over who can access the system. It was first introduced in CentOS 4 and improved in the later CentOS versions.
We’ll have to make changes to the SELinux policy to allow apache user access, and we’ll do this using the semanage command.
SEmanage is used to configure certain elements of SELinux policy without modifying or recompiling the policy resources. Semanage command can be used to adjust port context, file context, and booleans.
This allows us to browse the existing default context policies and create our own policies.
To enable the semanage command, we’ll install SELinux Policy Core Python Utilities, which contains semanage.
sudo dnf -y install policycoreutils-python-utils
You might face problems in deploying web applications on CentOS while not using the default Apache directories (for content or log). We can create custom policies to apply the proper SELinux context types to your files and directories. This will give you independence in the placement of your application files.
This will protect you if (for some reason) your context settings disappear. You can quickly solve the problem by running a context restore to get your application running again in no time!
Now we’ll create and apply the policy to allow Apache to read and write daloRADIUS files:
sudo semanage fcontext -a -t httpd_sys_rw_content_t "/var/www/html/daloradius(/.*)?" sudo restorecon -Rv /var/www/html/daloradius
Now daloRADIUS should be installed and working.
To access it visit http://your_server_ip_or_domain/daloradius. If you get an error then check to see if your browser changed http:// into https:// and change it back.
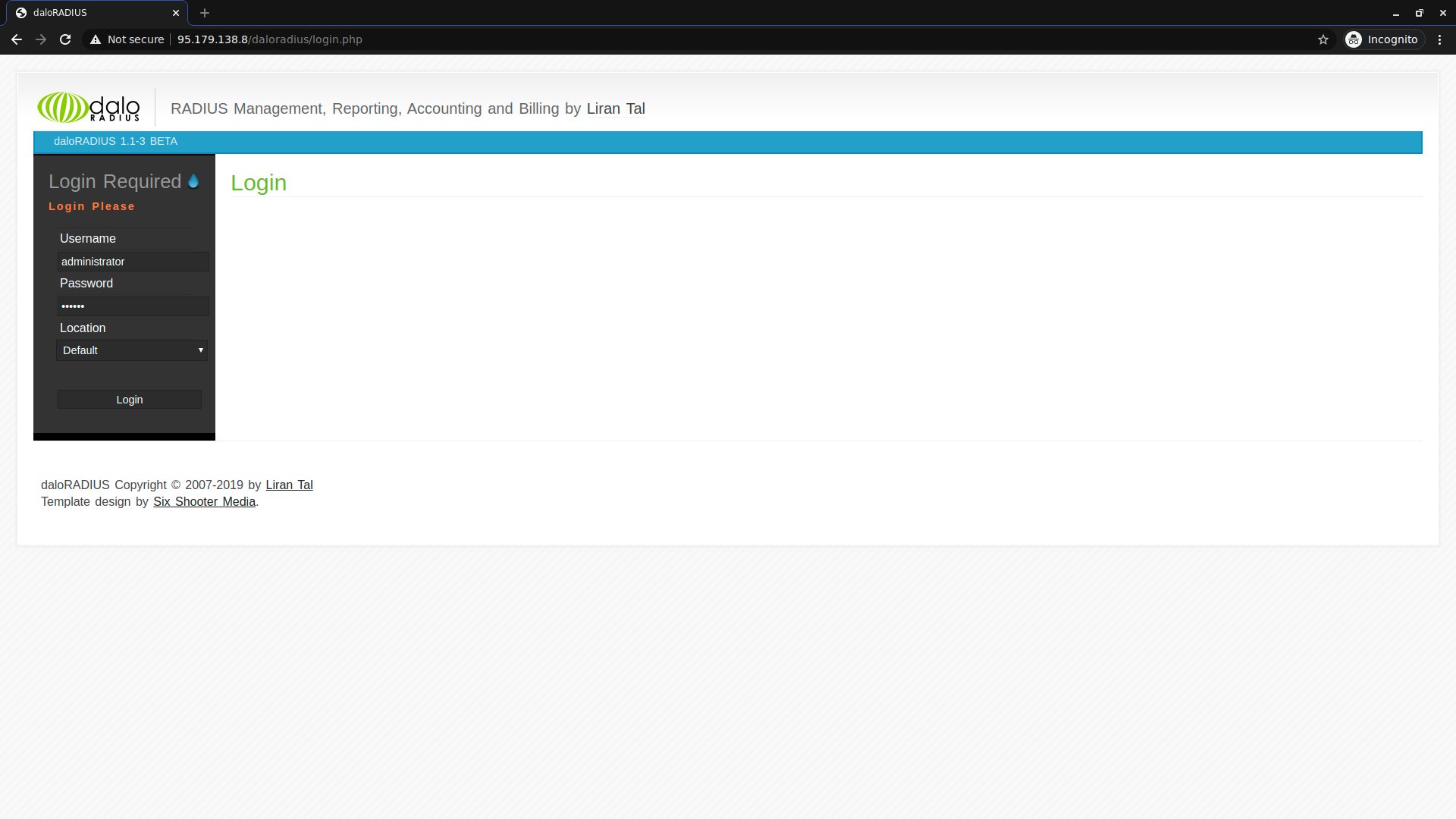
To login use the default daloRADIUS username/password:
username: administrator password: radius
Change daloRADIUS Administrator Password
Having a default login like administrator/password is a security vulnerability for anyone scanning for servers with daloRADIUS installed, so you’ll want to change you’ll want to at least change your password right away.
You can change it by logging into daloRADIUS > Config (In the top menu) > Operators (In the submenu) > List Operators (In the gray sidebar) > Click on administrator and in the next screen change the password and click Apply.
Testing daloRADIUS Web Panel
To test that FreeRADIUS and daloRADIUS are working, we’ll perform some basic operations in daloRADIUS and then send a test Authentication Request from another computer to our FreeRADIUS server.
1. Creating a NAS Client Table
The Network Access Server (NAS) client table acts as a gateway that guards a protected resource. For another computer to connect to our RADIUS server, it needs to be added to the NAS client table.
The NAS is an intermediary that a client connects to, then the NAS asks the resource (in our case the RADIUS server) if the credentials are valid, and based on this the NAS will allow or disallow access to the protected resource.
You can read a bit more about the NAS on this page from the FreeRADIUS wiki.
To create the NAS table, in the top menu navigate to Management, and in the submenu click on Nas. Then in the left sidebar click New NAS.
You’ll have to fill in the following:
NAS IP/Host: the IP or fully qualified hostname from which you’re trying to connect
NAS Secret: a password for connecting to the NAS, but it’s referred to as a secret. It’s used to communicate between the client/NAS and RADIUS server.
NAS Type: There are a few types that are recognized, including livingston, cisco, portslave. This is passed to the external checklogin program when it is called to detect double logins. For the purposes of this tutorial we’ll go for other.
NAS Shortname: An alias that can be used in place of the IP address or fully qualified hostname provided under NAS IP/Host
For our example we’ll fill in:
NAS IP/Host: IP of another computer we’re using as a client
NAS Secret: nobodywilleverlearnthissecret!!11!!
NAS Type: other
NAS Shortname: ProductionServer
2. Create a User
To create a user navigate in the top menu to Management, in the submenu Users, and next in the left sidebar New User.
We’ll just fill in Username and Password and leave the Password Type and Group as they are.
For our example we’ll fill in:
Username: new_customer
Password: customer_strong_passwd_123
There are more attributes to configure, but for the purpose of this tutorial we’re filling in basic info to get FreeRADIUS set up and working.
Now we can test our NAS table and user.
Important Note
Every time a NAS is added you need to restart FreeRADIUS so it fetches the updated table.
To test FreeRADIUS we’ll run it in debug mode so we can see the output when we try to connect with our newly created user.
The service is probably still running normally, so we’ll first stop it and then run it in debug mode as we’ve done when we first tested it:
Stop the radiusd service:
sudo systemctl stop radiusd
And run it in debug mode:
sudo radiusd -X
The output should be something like this:
[...] Listening on auth address * port 1812 bound to server default Listening on acct address * port 1813 bound to server default Listening on auth address :: port 1812 bound to server default Listening on acct address :: port 1813 bound to server default Listening on auth address 127.0.0.1 port 18120 bound to server inner-tunnel Listening on proxy address * port 41582 Listening on proxy address :: port 35140 Ready to process requests
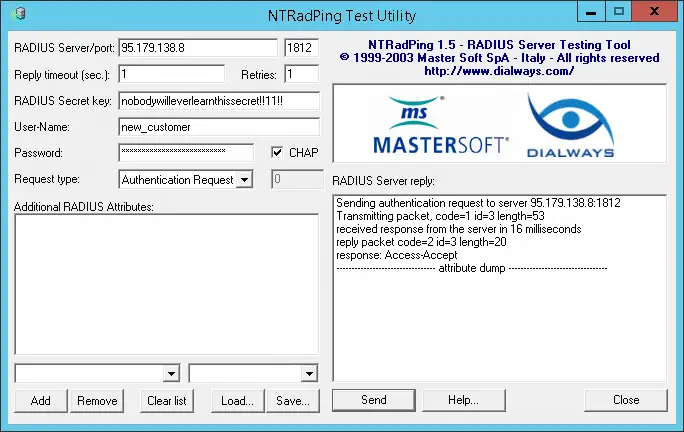
3. Test with NTRadPing
For convenience, we’ll test the server using a free software for Windows, called NTRadPing.
You can download it here https://community.microfocus.com/t5/OES-Tips-Information/NTRadPing-1-5-RADIUS-Test-Utility/ta-p/1777768. This is a direct link to the archive https://community.microfocus.com/dcvta86296/attachments/dcvta86296/OES_Tips/148/1/ntradping.zip
To run it just unzip the archive and run the executable.
This is how it looks like and how we’ll fill in the details in NTRadPing. We’ll use it to send an Authentication Request to the RADIUS server while it’s running in debug mode, so we can see first hand how it accepts the request.
We’ve filled the fields as follows:
RADIUS Server/port: IP of the server we have FreeRADIUS installed on / port 1812
Reply timeout (sec.): 1
Retries: 1
RADIUS Secret key:
User-Name: new_customer
Password: customer_strong_passwd_123
Lastly check the CHAP checkbox. This is so the request is made using a CHAP password, instead of the default PAP password.
Now you can test the RADIUS server. Just click Send in NTRadPing and if you get an Access-Accept response we can assume it’s working.
The output should look something like this:
Sending authentication request to server 95.179.138.8:1812 transmiting Packet, code=1 id=3 length=53 recieved response from the server in 16 milliseconds replay packet code=2 id=3 length=20 response: Access-Accept -------------------attribute dump------------------
FreeRADIUS FAQ
What is FreeRADIUS used for?
FreeRADIUS is an open-source implementation of the RADIUS protocol server that is mainly used to authenticate various types of network access.
FreeRADIUS provides protocols for:
- Authorisation
- Authentication
- Accounting
What is a RADIUS server and how does it work?
RADIUS is short for Remote Authentication Dial-in User Service. It’s a networking protocol that provides AAA (authorisation, authentication, and account) management protocols. The radius server works on the application layer and uses TCP/UDP protocols on the transport layer.
What are some RADIUS server use cases?
The RADIUS server is a client/server protocol and software. It enables remote access servers to communicate with a central server in order to authenticate users and authorize their access to the requested server or network.
Revisions & Updates of this Article
[April 12 2021]: Updated the /etc/freeradius/3.0/mods-enabled/sql editing section to mention commenting out the TLS block when configuring FreeRADIUS to use MySQL, as it is beyond the scope of this article.
[May 4 2021]: Added mention that you need to create the daloradius.conf.php file by copying daloradius.conf.php.sample.
Conclusion
Well done. You’ve set up FreeRADIUS, configured it to use MySQL or MariaDB, along with daloRADIUS, on a CentOS 8 server.
If you have any issues then contact us and we’ll try to help as soon as we can.
Skip the setup and instantly deploy a pre-configured FreeRADIUS server with MySQL and daloRADIUS in seconds. Our solution is secure, fully configured, and designed to save you time.
Your servers, managed for you, so you can focus on your business.
Need a custom solution? Our expert team is available for hire. Feel free to contact us.



Excellent article. I followed it mostly on the Ubuntu server and everything works, other than one issue. If I add any user account via daloradius GUI, it gets pushed into SQL radcheck table, but if I have any users added directly into MySQL via CLI, they are not fetched by the daloradius GUI. Is this by design?
Thanks
Yes, this is by design.
daloRadius users have more information stored like email and name. That information is stored in a different table.
The radcheck table only contains the information needed by Radius.
If you want to add users by CLI make sure to also insert them in the daloradius user table, Not sure what the name of the table is right now but it should be pretty easy to find once you look for it.
Good Day SteliXD;
Thanks for the tutorials truly being helpful for me as a student. i have install centos8 and follow instructions as given and just created mysql database but im now face with this error after restarting the radiusd.service.
rlm_sql_mysql: libmysql version: 10.5.5
mysql {
tls {
ca_file = “/etc/ssl/certs/my_ca.crt”
Unable to check file “/etc/ssl/certs/my_ca.crt”: No such file or directory
/etc/raddb/mods-enabled/sql[87]: Failed parsing configuration item “ca_file”
/etc/raddb/mods-enabled/sql[27]: Instantiation failed for module “sql”.
i am new to this can you kindly assist me as i am doing as a lab project.
Hi Jared,
Apologies for the late reply.
I believe this is because when configuring the /etc/freeradius/3.0/mods-enabled/sql file, there is also a TLS section that needs configured.
I updated the article to specify to comment out that TLS section.
Can you please check go to https://bytexd.com/freeradius-centos/#configure-freeradius-to-use-mysql-mariadb and to point 3?
It starts with “If we use MySQL the FreeRADIUS configuration assumes the use of TLS certs by default” and it shows how to locate the TLS section and comment it out.
Let me know how it goes?
EDIT: I corrected the link I provided, as I initially linked a similar section on configuring TLS from a different tutorial.
Good Day and thanks SteliXD;
Many thanks for the respond and the information being provided, had to revisit the site to see your respond and sorry for such a late update. have also follow updated instruction including commenting
mysql {
# If any of the files below are set, TLS encryption is enabled
# tls {
# ca_file = “/etc/ssl/certs/my_ca.crt”
# ca_path = “/etc/ssl/certs/”
# certificate_file = “/etc/ssl/certs/private/client.crt”
# private_key_file = “/etc/ssl/certs/private/client.key”
# cipher = “DHE-RSA-AES256-SHA:AES128-SHA”
# tls_required = yes
# tls_check_cert = no
# tls_check_cert_cn = no
#}
still having the same error as before, please assist me as ive share my email and look forward to getting help in completing my very first freeradius project as these experiences and lessons im learning on this journey i wouldn’t forget anytime soon
Good Day SteliXD;
Many Thank for the tutorial, like i mention in my reply previously i still had the same problem after commenting out the tls files but i also notice that the issues i had was due to permission in creating said file with the 644, there a file in the /var/www/html/library call daloradius.conf.php.sample that i rename and noticed that the issues i was having is done. really appreciate the tutorials and look forward to learning more.
Regards,
SteliXd ive also noticed that everytime the server reboots the radiusd.service failed, can you please share command to have it start when the server boot up, ive search and try others guide but still radiusd.service keeps failing. currently this the issues and i have restart the entire process and still the same.
Hi Jared,
Apologies for the late reply and for the issues you have been having.
You are right to copy the daloradius.conf.php.sample. I now realize that the daloRADIUS package was updated after this article was written, and since then you have to copy the sample file to create daloradius.conf.php
I updated the guide thanks to you and will also update the video when I can, but have added a warning just before the video, for future readers.
Again, I very much apologize for not updating this article sooner.
—
Regarding radiusd.service not starting.
The command that should’ve enabled it to start on boot is `sudo systemctl enable –now radiusd.service`
Are you seeing any errors?
Hi,
I would like to enable google authenticator on top of this? But I have no clue where to start? Can you give me any pointers in the correct direction.
Hi Tom,
I haven’t tried this myself and am unable to at the moment, otherwise I’d go through the steps myself.
I can’t guarantee it, but this tutorial looks promising at first glance https://networkjutsu.com/freeradius-google-authenticator/
It’s from 2016 but I’m thinking it may be a step in the right direction.
I am having this error due to which uses online session not displaying .. plz help ..
ERROR: (24) sql: ERROR: rlm_sql_mysql: ERROR 1054 (Unknown column ‘framedipv6address’ in ‘field list’): 42S22
Hi Sujan,
It looks to me like the radacct table doesn’t have the frameipv6address, which it should have gotten after you imported the database schema for the FreeRADIUS MySQL module.
Can you try adding that column manually?
Log into MySQL:
Once logged in select the radius database:
And add the columns to the radacct table:
ALTER TABLE radacct ADD COLUMN framedipv6address varchar(45) NOT NULL default ”;
And then exit the MySQL console and try again.
Let me know if it works out?
Good Day SteliXD,
Thanks again for the response and update to your page, appreciate that you’ve been a help all along this journey. Will appreciate if you do a toturials on how to join a mikrotik router to be authenticated by the DaloRadius.
I’m getting Access-Reject, but this was the best tutorial so far.
Great article to follow for someone who doesn’t work on servers, much less linux based servers. For the daloradius portion of the article, when I hit /daloradius/login.php I get commands displayed for login.php and not the html version of it.
Everything installed successfully without any error, but when I tried to login DALORADIUS then its shows me the error after enter username and passowrd on the login screen of Daloradius.
Database connection error
Error Message: DB Error: extension not found
Hi.
This is Kashif, This article is good and comprehensive. I can’t find any error installing everything, but I’m not ablt to login DALORADIUS GUI interface, and getting this error
Database connection error
Error Message: DB Error: extension not found
Please do help
Hi Kashif,
Apologies for the delay!
I’m not 100% sure here. One thing I can think if is to check /var/www/daloradius/library/daloradius.conf.php and make sure that instead $configValues = ‘10.101.0.10’; you have $configValues = ‘localhost’;
I picked this up from here
Let me know if that works, please?
Pelase check attach file, its localhost already
Apologies for the delay, Kashif.
I went through the tutorial again on a fresh server and it seems to be working for me.
Would it be possible for you to go through the tutorial again, in case you missed something?
Also what distro are you using, and what PHP version?
I tried again and its get same Error, can you send me the active link for CentOS 8, becuase used CentOS8 Stream and its getting error when I using this command:-
dnf module list freeradius
Errors during downlading metadata for repository ‘appstream’ Status code 403